Phishing is a scam employed by cybercriminals using the Internet Bypass.apk. Phishing attacks use various means. However, the most common mean is email.
This technique uses fake communications, called “social engineering” to steal information or install malware by exploiting natural human trust dell omsa. The phishers then use that information to commit identity theft usually for financial gain but sometimes for political purposes. Day to day, the attackers are making their techniques more sophisticated, making it harder to detect, eventually rising the number of victims at an alarming rate 터치다운.
This scam is a real threat and costs the annual economy more than three billion dollars, in addition to direct financial loss as well as the costs to repair the security breaches, restore the damaged reputations, and regain the customer’s confidence 배재콕 다운로드. Moreover, no company wants to consider the potential audit findings for failing to address phishing attacks, given the regulatory environment.
How Phishing Works Download Harry Potter Fire?
For phishing to work effectively, the phisher sends a convincing but fake mass email that appears to come from a trustworthy source such as emails from friends & co-workers, financial institutions, and online retailers and social media sites like Facebook Crownfish.
Be wary of phishing hooks, after sending out a phony message, phishers wait and see who falls into the trap. Usually, email recipients without proper email phishing protection are allured by the attackers to confirm their username and password, social security number, bank account number, or disclose other personal information 원오크락.
Phishing usually requires human interaction to work such as clicking a link downloading and installing software or opening an attachment. Unfortunately, even small actions or negligence in protection against phishing can have far-reaching consequences Download Freddy's Pizzeria. Advanced phishing techniques have more severe consequences such as installing hidden malware programs that are hard to detect and remove.
A phishing email may look harmless but one wrong move can open a Pandora’s Box of electronic evil, for which the individuals and companies are required to take considerable measures for protection from phishing Mime.
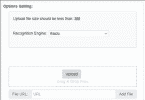
There are numerous phishing protection softwares available in the market that claim to provide ultimate phishing email protection. However, they are either expensive or ineffective against advanced techniques (other than emails), causing considerable losses to the victims pyqt designer 다운로드.
How to avoid phishing?
Fortunately, there are several methods for phish protection that can help you avoid phishing scams effectively and inexpensively. Some of them are as follow:
- Be very cautious while sharing your personal information including username, and passwords, on any website, or someone on call or email.
- Don’t click on links, provided on emails, messages, or websites, from the people or organizations you don’t know.
- If you receive an email, call or message from a trustworthy company or a friend, that appears to be suspicious, then you must contact them via legitimate sources and ask for the proper explanation for the content or link you have received.
- Use spam filters, or blacklist functions to prevent such malicious texts and emails from reaching you.
- Federal Trade Commission has also issued a FTC consumer info on Phishing to guide the masses against these attacks.





Leave a Comment